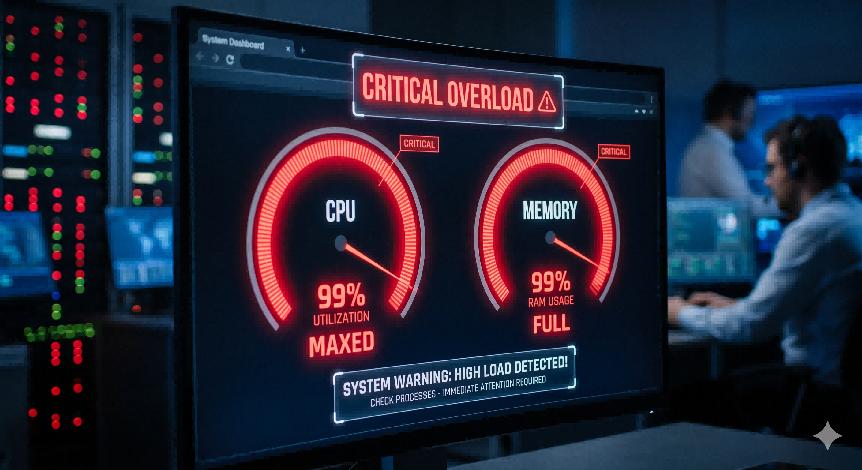
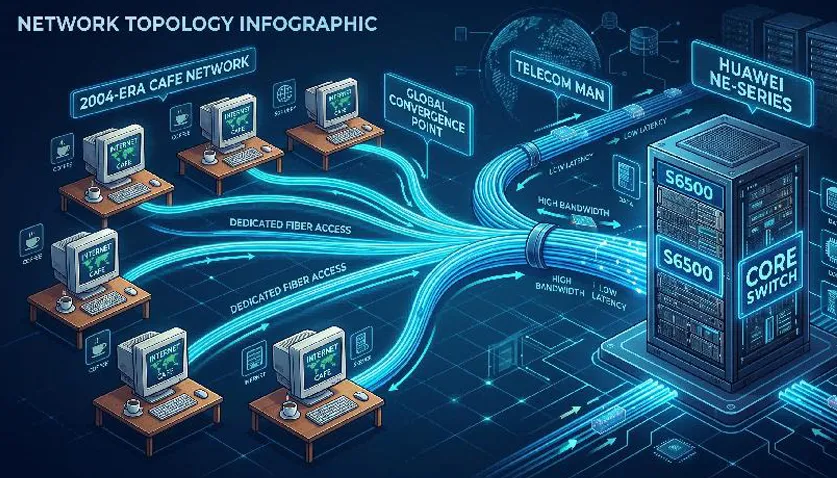
Before the routing abnormality issue was fully resolved, the fifth tribulation struck! Following the recommendation of the S6500 R&D team, the routine inspection tasks of the S6500 support team were updated to include monitoring of the S6500 CPU utilization and memory utilization. As expected, inspections revealed that the S6500 at many nodes suffered from excessively high CPU utilization and overly high memory utilization.
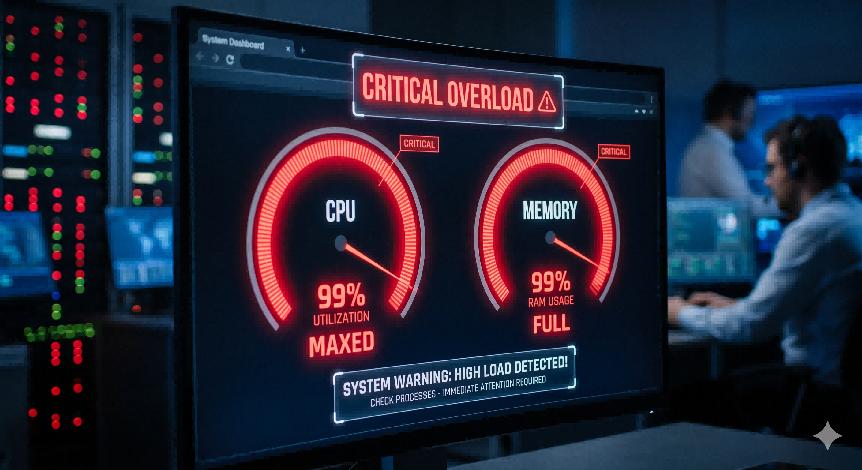
Engineers from the S6500 support team collected information from the S6500 devices with abnormally high CPU utilization in accordance with R&D guidance and promptly submitted the data to the S6500 R&D team.
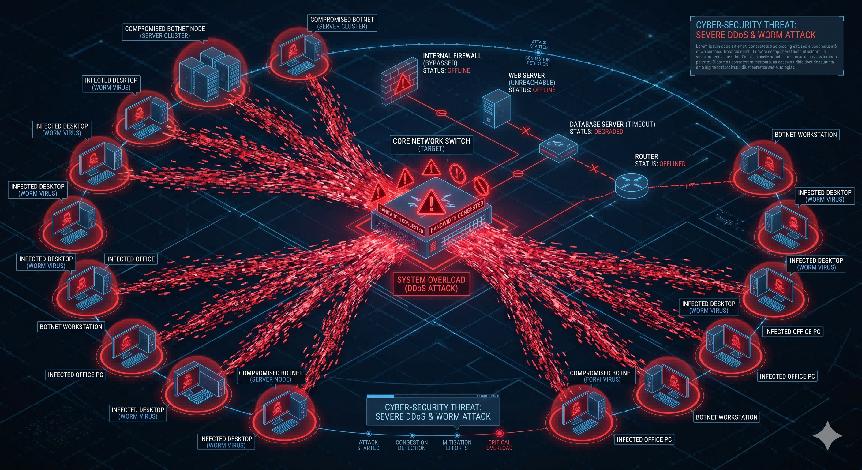
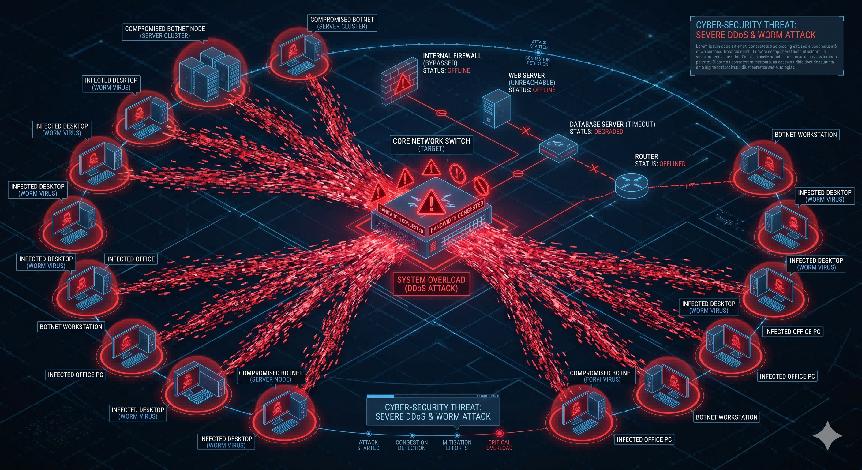
After analyzing the information collected from multiple nodes, the S6500 R&D team reached a final conclusion: the issue was caused by worm virus attacks on the network.
The period from 2003 to 2007 marked the peak of Internet worm outbreaks. Many highly impactful worms emerged during this time, including Worm.Blaster, Shockwave, Zotob, MSN virus, Worm.Viking.dr (also known as Panda Burning Incense), and others.
Worm outbreaks affect network devices mainly in the following aspects:
Massive bandwidth consumption: Worms generate huge network traffic through automatic scanning and propagation, causing bandwidth congestion and even paralyzing LANs or backbone networks in severe cases.
Degraded or crashed network device performance: Infected devices such as routers and switches process a large number of abnormal requests, leading to CPU overload and memory exhaustion, which may result in service interruption or device reboot.
Network service outages: Worms may exploit device vulnerabilities (such as TR�064/069 protocol flaws) to control network equipment, shut down critical ports, or launch DDoS attacks, causing large-scale network disconnections.
Expanded propagation scope: Worms can spread laterally through network shares, USB drives, weak passwords, and other channels, infecting peripherals like printers and NAS to further enlarge the attack surface.
Stealth control and backdoor implantation: Some worms implant backdoors after infecting devices, turning them into botnet nodes for continuous remote control and subsequent attacks.
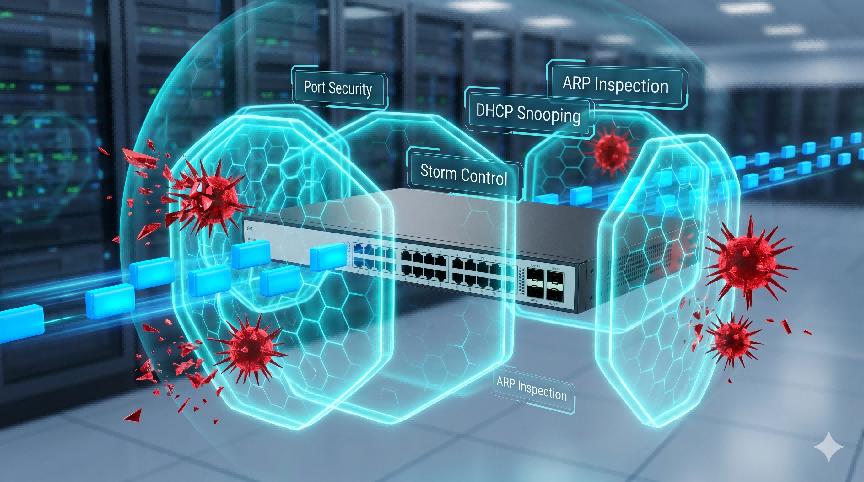
After confirming that worm virus attacks could lead to critical risks such as excessively high CPU utilization and memory exhaustion on the S6500, the S6500 R&D team released a targeted software version. The version added CPU protection mechanism and memory protection mechanism, and further integrated features including Port Security, Storm Control, DHCP Snooping, and ARP Inspection to effectively mitigate the impact of worm viruses on the stable operation of the S6500.
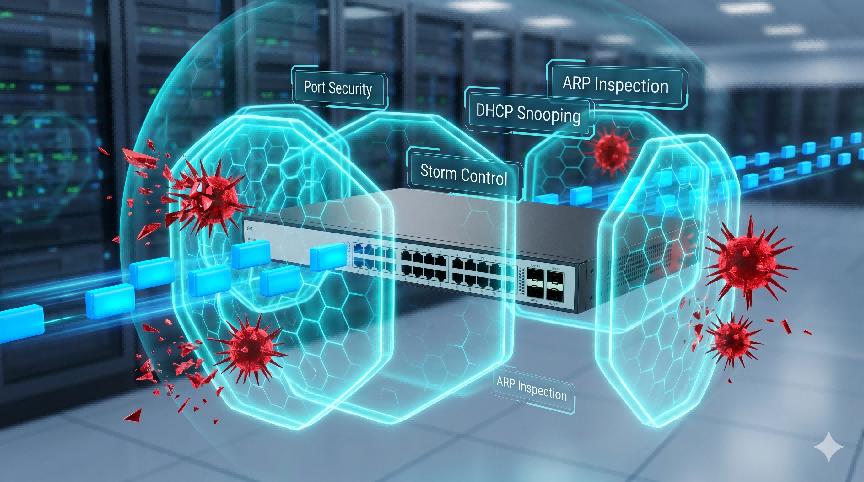
The S6500 trial support team then upgraded the software version on all S6500 switches at the 112 trial nodes, overcoming both the fourth and fifth tribulations.
By Lanbras
Lanbras specializes in translating cutting-edge optical and Ethernet transmission technologies into clear, valuable insights that help our customers stay ahead in a fast-evolving digital world.
By turning complex technical concepts into practical, business-driven content, we aim to empower decision-makers with the knowledge they need to make confident, future-ready choices.
 Internet Data Center
Internet Data Center FAQs
FAQs Industry News
Industry News About Us
About Us Data Center Switch
Data Center Switch  Enterprise Switch
Enterprise Switch  Industrial Switch
Industrial Switch  Access Switch
Access Switch  Integrated Network
Integrated Network  Optical Module & Cable
Optical Module & Cable 





 Call us on:
Call us on:  Email Us:
Email Us:  2106B, #3D, Cloud Park Phase 1, Bantian, Longgang, Shenzhen, 518129, P.R.C.
2106B, #3D, Cloud Park Phase 1, Bantian, Longgang, Shenzhen, 518129, P.R.C.